Peer-to-Peer Debugging: The Senior Colleague’s Diagnostic Probe
Why “just fixing it” for your teammate is a failure of senior leadership.
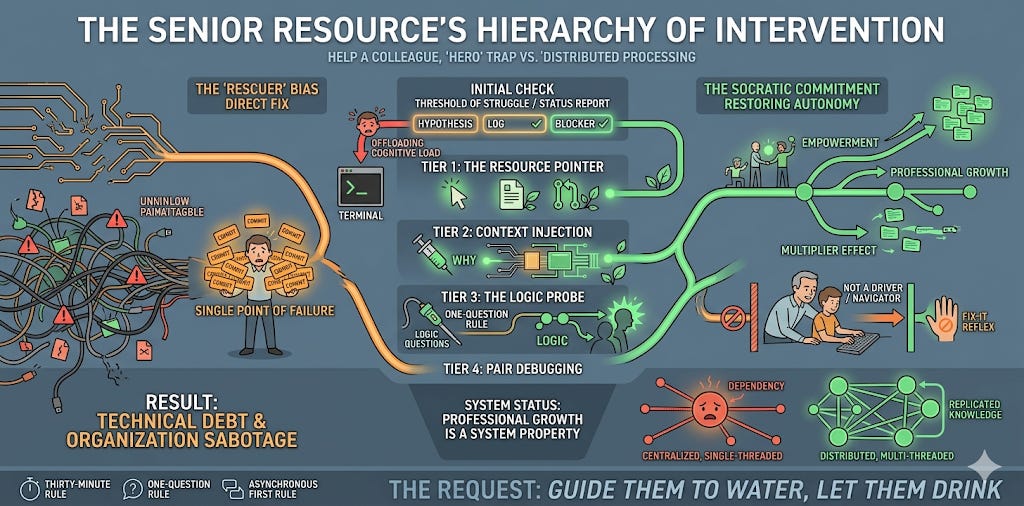
When a colleague approaches you with a blocker, your primary goal is not to fix the bug. Your goal is to restore the peer’s autonomy. If you provide the solution directly, you have fixed the code but broken the engineer. You have traded a short-term commit for long-term dependency.
For a senior resource, “helping” is a high-cost operation. You are diverting your high-level compute cycles to a local execution problem. To ensure this resource allocation is efficient, you must follow a tiered intervention protocol.
Operating Conditions: The Threshold of Struggle
Before engaging, you must establish if the peer has met the Threshold of Struggle. If you intervene too early, you prevent the struggle required for deep learning. If you intervene too late, you have allowed the system to remain in a deadlocked state for too long.
The Request is simple: before you offer any help, require the “Status Report.” This is a three-point data packet the peer must provide:
The Current Hypothesis: What do they think is happening?
The Debugging Log: What specific actions have they already taken to verify that hypothesis?
The Specific Blocker: Is it a lack of knowledge, a lack of access, or an architectural ambiguity?
If they cannot provide this packet, they are not ready for help. They are just offloading their cognitive load onto you. Send them back to the terminal.
The Hierarchy of Intervention
Instead of jumping to the fix, apply the minimum necessary force. You are a senior resource, and your time is expensive. Use this hierarchy to provide technical leverage without taking the keyboard.
Tier 1: The Resource Pointer. This is your most efficient move. You provide a link to the technical documentation, a specific file in the repository, or a previous Pull Request that handled similar logic. The goal here is to de-silo knowledge. By pointing the way, you allow the peer to continue solo. This reinforces their ability to find information without your direct intervention in the future.
Tier 2: Context Injection. If the documentation exists but the peer is still stuck, the issue is likely a lack of architectural context. You explain the “why” behind the design. For example, you explain that a specific pattern was used because of a hard hardware constraint or a legacy dependency. This updates their mental model. Once the peer understands the “why”, they can usually correct their own course without further assistance.
Tier 3: The Logic Probe. This is where you use the Socratic method. You ask a leading question that exposes a flaw in their mental model. Instead of showing them the bug, you ask how the system handles a specific edge case or a null response. This forces the peer to discover the fix themselves. It is a high-leverage move because the knowledge is earned, not given.
Only when these three tiers fail do you move to Tier 4: Pair Debugging. This is your most expensive operation. You sit with the peer, but you act strictly as the navigator. You are never the driver. Your hands stay off the keyboard. You guide the investigation while they execute the commands and type the code.
Failure Mode: The “Rescuer” Bias
The biggest risk in peer help is the “Rescuer Bias.” This is the internal ego-drive to show off how fast you can solve a problem. It feels like “being a team player.” It is actually a form of organizational sabotage.
When you “rescue” a peer, you are effectively telling them that their time is less valuable than yours. You are also signaling that they are incapable of solving complex problems. This destroys the team’s “bus factor” and forces every interesting problem to eventually route through you. You become the single point of failure. You are now the bottleneck.
Proposed Fix: The “Socratic” Commitment
Replace your “fix-it” reflex with a coaching protocol. Treat every request for help as a ticket that needs to be resolved through empowerment, not execution.
Implement a “Thirty-Minute Rule”: Peers must struggle for 30 minutes, but no more than 60, before asking for a consult. This ensures they have a “debugging log” to present.
The “One-Question” Rule: Try to help using only one question. “What happens if you trace the data back to the entry point?” or “How does this handle a null response?”. Often, this is the only push they need.
The Asynchronous First Rule: If the help isn’t an emergency, ask for the problem to be written down in a shared thread. Writing the problem down often solves it (Rubber Ducking) and creates a searchable record for the next person who gets stuck.
System Status: Professional Growth is a System Property
A team’s strength is not the sum of its individuals. It is the quality of the connections between them. If those connections only flow in one direction—from junior to senior—the system is fragile.
When you use the “How can I help?” diagnostic, you are strengthening the nodes of your team. You are building a distributed system where knowledge is replicated across all instances. This is how you scale. This is how you make yourself promotable.
The Request: This week, do not touch a peer’s keyboard. Not once. Use the Tiered Intervention Protocol. Guide them to the water, but let them do the drinking.
Share Your Stack Traces
Tell me about the time you “helped” so much that you ended up owning a piece of code forever because no one else learned how to maintain it. Or, share a Tier 3 question that once helped you see a problem in a completely new light. Post your telemetry in the comments.
System Library: Further Reading
Tools for peer leadership and technical mentorship.
The Concept: The Multiplier Effect by Liz Wiseman
The Engineering Angle: Specifically, study the “Accidental Diminisher” known as The Rescuer. This is the senior engineer who jumps in to fix every bug, effectively drowning the team’s ability to learn. It is a fatal operational error.
The Video: David Marquet: How Great Leaders Serve Others
The Gist: A former submarine commander explains how to solve the “Hero” bottleneck. He implemented a protocol where subordinates state their intent rather than asking for permission. This is a high-reliability communications protocol designed to eliminate the single point of failure in leadership. It is the definitive guide for seniors who want to scale their impact without taking the keyboard.
The Book: Talking with Tech Leads by Patrick Kua
The Takeaway: A collection of perspectives on shifting from “best coder” to “effective leader of coders.”
System Status: Critical?
Writing about management is theory. Fixing it is engineering.
If your organization is suffering from knowledge silos, hero-culture, or structural debt, I provide Strategic Debugging and Leadership Mentoring.
Review my operating parameters at weivco.com.